🚨 URGENT: “ClickFix” Phishing Campaign Targeting Las Vegas HospitalityCopy-Paste PowerShell Scam Bypasses Email Filters – Hotels, Casinos, and Transportation at Risk |
|
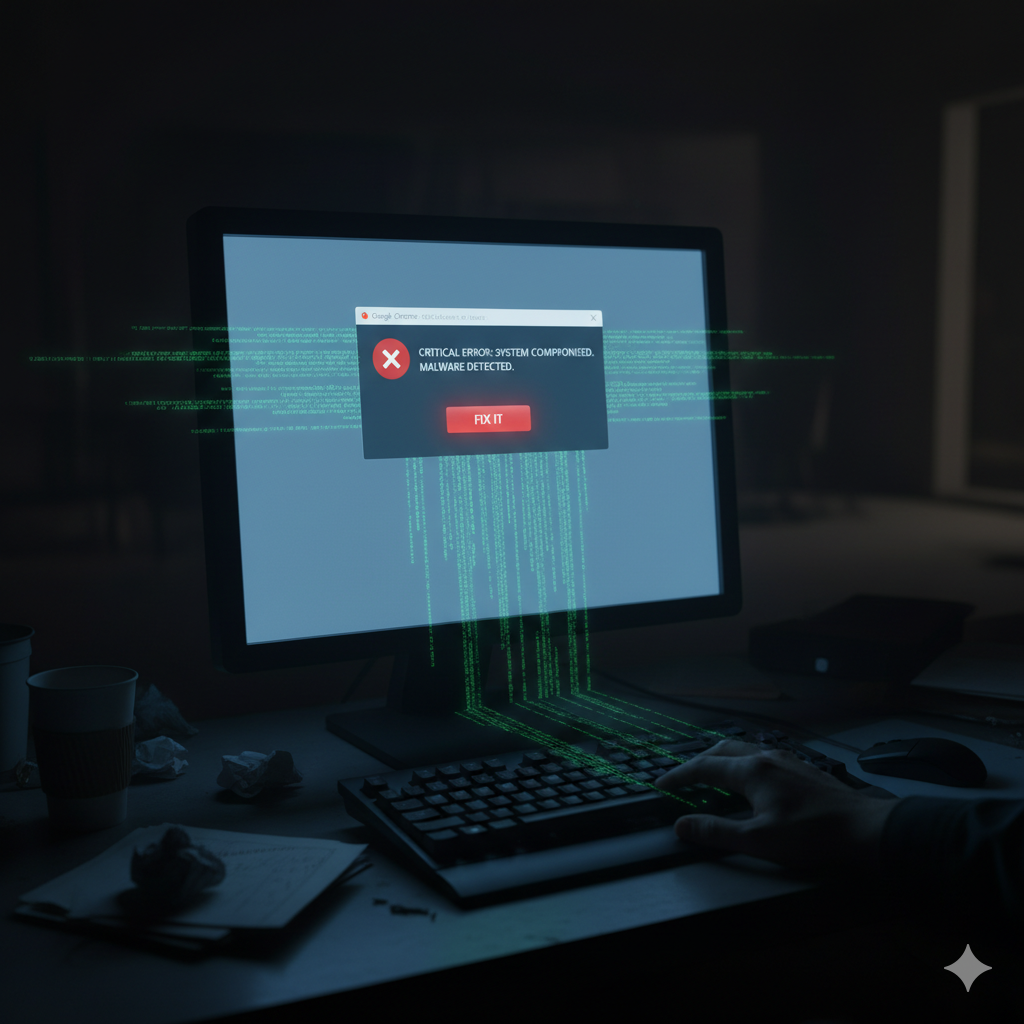
1. Executive Summary: The “Copy-Paste” TrapA sophisticated new social engineering campaign, dubbed “ClickFix,” is actively targeting the hospitality and transportation sectors. Unlike traditional phishing that relies on a malicious link, this attack weaponizes “tech support anxiety.” |
How The Scam Works:The Trap: Employees see a fake pop-up (mimicking Google Chrome, Microsoft Word, or Booking.com) claiming a “Critical Error” or “Update Required.” Instead of a download button, it instructs them to copy a PowerShell script and paste it into their terminal to “fix” the issue. The Impact on Las Vegas: With our city’s heavy reliance on Booking.com, Expedia, and rapid front-desk operations, this specific campaign puts guest data and corporate networks at immediate risk of ransomware and credential theft. Hotels on The Strip, downtown properties, and casino resorts are prime targets. |
2. The Technical Details: Bypassing Email FiltersThis attack is clever because it bypasses email filters—the malicious code is never “sent” to you; you paste it yourself. |
Attack Mechanism Analysis:
|
3. The Risk: Why Firewalls Can’t Stop ThisFor a Las Vegas hotel manager or logistics coordinator, this looks like a standard IT glitch. The attack exploits trust in familiar platforms and the pressure of fast-paced hospitality operations. |
🛡️ Bypassing EDR (Endpoint Detection & Response)Because the user manually executes the script, many Endpoint Detection & Response (EDR) tools view it as an “administrative action” rather than a virus. The malware uses legitimate Windows utilities (Living off the Land – LotL attack), making detection extremely difficult. Traditional antivirus sees PowerShell.exe and assumes it’s a technician performing maintenance. |
🔐 Session Token TheftThe malware targets browser cookies and session tokens. This means hackers can log into your Booking.com, Expedia, or Bank of America portal without needing your password or 2FA code. They hijack active sessions, appearing as legitimate logged-in users. Multi-Factor Authentication provides zero protection against session token theft. |
💳 Guest Fraud & Reputation DamageOnce inside a hotel’s Booking.com account, attackers can message future guests demanding payment to alternative accounts, cancel reservations causing revenue loss, or steal guest credit card information for fraud. This is a reputation nightmare for Las Vegas properties. A single incident can destroy years of 5-star reviews and guest trust, particularly damaging for boutique hotels and independent properties. |
Las Vegas Hospitality Sector Vulnerability:
|
4. The 3-Step Mitigation PlanSince this exploits human behavior, technology alone isn’t the fix. You need a “Human Firewall.” |
|
|
|
5. How CMIT Solutions Protects Las Vegas HospitalityWe actively hunt for these specific “Living off the Land” (LotL) attacks where hackers use your own tools against you. Our hotel and casino clients receive specialized protection designed for high-volume guest operations. |
Hospitality-Focused Security Services:
|
⚠️ Is Your Front Desk Vulnerable to “Fake Update” Scams?Don’t let ClickFix compromise guest data and destroy your reputation. We can assess your front-desk security in 24 hours. |
Protect Your Hotel from ClickFix AttacksGet specialized hospitality cybersecurity that protects guest data, Booking.com credentials, and your reputation. CMIT Solutions: Trusted by Las Vegas Hotels, Casinos, and Hospitality Groups |
Key Takeaways for Hospitality Operations:
|
6. Source & Technical AnalysisRead the technical breakdown of the ClickFix campaign targeting hospitality here: The Hacker News: Large-Scale ClickFix Phishing Attacks Target Transport and Hospitality Sectors |