By the time an audit shows up on the calendar, it’s already too late to get organized.
Most businesses don’t fail audits because they ignore compliance requirements. They fail because they can’t prove that their controls, policies, and security practices are consistently followed. The work is being done but the evidence isn’t always there when it matters.
Audits don’t evaluate effort or intent. They evaluate documentation, consistency, and traceability. If your systems can’t clearly show what’s happening behind the scenes, even strong compliance programs can look weak under scrutiny.
This article breaks down how to build audit-ready evidence into your everyday IT operations so audits become routine validations, not stressful fire drills.
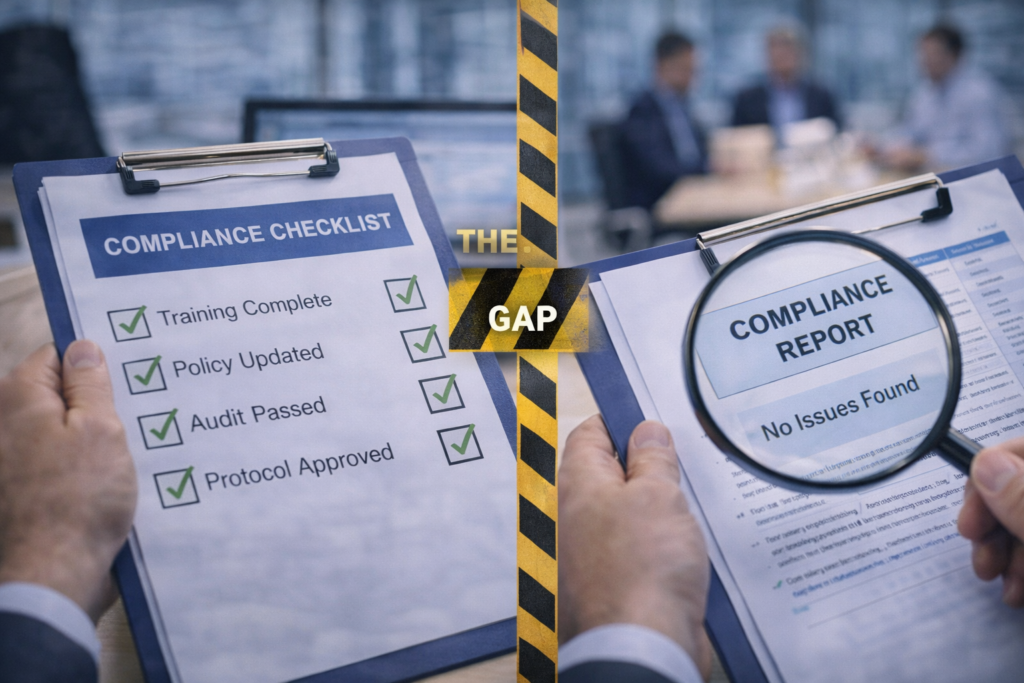
The Gap Between Compliance Efforts and Verifiable Proof
Many organizations believe they’re compliant because they have:
- Written policies
- Security tools in place
- Access controls configured
- Backups running
- Monitoring enabled
The problem isn’t the absence of controls. It’s the absence of centralized, consistent proof that those controls are working as intended over time.
When evidence is scattered across inboxes, spreadsheets, or individual systems, it becomes difficult to demonstrate compliance clearly. Auditors aren’t looking for explanations, they’re looking for records that confirm your claims.
Closing this gap requires shifting from “we do this” to “we can show this.”
What Auditors Expect to See During an Audit
Auditors are not trying to catch organizations off guard. Their goal is to confirm that what you say is happening is actually happening.
They expect to see:
- Clear, up-to-date policies
- Controls that align with those policies
- Repeatable processes
- Evidence that is easy to retrieve and verify
What raises concerns:
- Documentation created just before the audit
- Policies that don’t match operational reality
- Manual explanations without system logs
- Inconsistent or missing records
The strongest audit outcomes come from simple, predictable systems that generate evidence automatically.
Access Control Evidence That Aligns With Your Policies
If your organization claims role-based access control, you need more than configuration settings you need proof.
Audit-ready access control evidence includes:
- A clear record of who has access to what systems
- Documentation showing why access was granted
- Logs that track when access was added, modified, or removed
- Proof of regular access reviews
When access management is centralized and documented, this evidence can be produced quickly. When it’s handled informally, it becomes one of the most common audit pain points.
Patch Management Documentation That Demonstrates Consistency
Automated patching reduces risk—but audits still require visibility.
Auditors want to see:
- Defined patch schedules
- Reports showing patch deployment status
- Exception handling for systems that couldn’t be patched
- Evidence that vulnerabilities are addressed in a timely manner
Without documentation, even well-patched environments can appear unmanaged. Consistent reporting turns patching from a claim into verifiable proof.
Backup and Recovery Evidence That Goes Beyond “Yes, We Back Up”
Backups are a critical compliance requirement, but they’re only valuable if you can prove they’re working.
Audit-ready backup evidence includes:
- Automated backup success reports
- Monitoring alerts for failures
- Documentation of recovery testing
- Clear retention policies
Auditors want confirmation that backups are not only running, but also being monitored and tested. Assumptions don’t pass audits records do.
Security Monitoring and Incident Response Proof
If your organization claims continuous security monitoring, auditors will expect to see evidence of activity.
This includes:
- Logs showing alerts generated
- Incident records tied to those alerts
- Response timelines
- Resolution documentation
The goal isn’t to show a high volume of incidents. It’s to demonstrate that when something happens, it’s detected, investigated, and addressed in a structured way.
Traceability matters more than complexity.
Policies That Reflect Actual Day-to-Day Operations
One of the most common audit findings is policy misalignment.
For example, if a policy states that access reviews occur quarterly, there must be evidence that:
- Reviews happened on schedule
- Findings were documented
- Changes were implemented when needed
Audit-ready organizations avoid aspirational language. Their policies describe what actually happens and their systems generate proof to match.
Why Last-Minute Audit Preparation Creates Risk
Trying to assemble evidence weeks before an audit often leads to:
- Missing documentation
- Inconsistent records
- Rushed policy updates
- Gaps discovered under pressure
Audit readiness isn’t something you turn on temporarily. It’s the result of building evidence into everyday operations.
When documentation is created as work happens, audits become confirmation exercises instead of high-stress events.
What Audit-Ready Operations Look Like in Practice
Organizations that handle audits well share common traits:
- Centralized logging and reporting
- Automated security and maintenance tasks
- Consistent documentation practices
- Clear ownership of controls
- Easy access to evidence when requested
In these environments, audits are predictable, efficient, and far less disruptive.
How Managed IT Services Support Audit-Ready Evidence
This is where CMIT Solutions of Boston, Newton & Waltham plays a critical role.
Audit readiness is both a compliance challenge and a systems challenge. A managed IT services provider helps by:
- Centralizing security logs and reporting
- Automating patching, backups, and monitoring
- Aligning technical controls with compliance requirements
- Maintaining documentation continuously
- Reducing reliance on manual evidence collection
- Identifying gaps before auditors do
The result is stronger compliance with less internal effort.
Conclusion: Compliance Confidence Comes From Proof
Strong compliance programs aren’t built on promises or last-minute preparation. They’re built on systems that generate evidence naturally, consistently, and securely.
When your IT environment supports compliance by design, audits stop being disruptive events and become routine validations of work already being done.
The difference isn’t effort, it’s structure.
Ready to Strengthen Your Audit Readiness?
If your organization isn’t confident it can produce audit evidence quickly and consistently, now is the time to address it before the next audit cycle begins.
CMIT Solutions of Boston, Newton & Waltham helps organizations build audit-ready IT environments that support compliance, reduce risk, and stand up to scrutiny.
Schedule a discovery call today and find out how to turn your compliance efforts into defensible, audit-ready proof without adding complexity to your operations.
Because when auditors ask, “Can you show me?”
You should already have the answer.