Phishing has been around for decades, but today’s attacks are far more sophisticated than the clumsy scams of the past. Modern cybercriminals leverage artificial intelligence, social engineering, and advanced spoofing techniques to craft emails that look and even feel legitimate. For small and mid-sized businesses (SMBs), this evolution means that traditional spam filters are no longer enough.
Here’s how phishing scams are changing, what’s at stake for your company, and the practical steps your team can take to stay one step ahead.
The New Face of Phishing
Phishing is no longer limited to badly written emails claiming you’ve won a lottery. Today’s threats are carefully designed to exploit human behavior:
- Business Email Compromise (BEC): Hackers impersonate executives or vendors to request urgent wire transfers or confidential data.
- AI-Generated Emails: Artificial intelligence creates perfectly worded messages that mimic real conversations.
- Smishing & Vishing: Phishing attacks now extend to text messages and phone calls.
- Multi-Stage Campaigns: Hackers send harmless messages first to build trust before delivering malicious links.
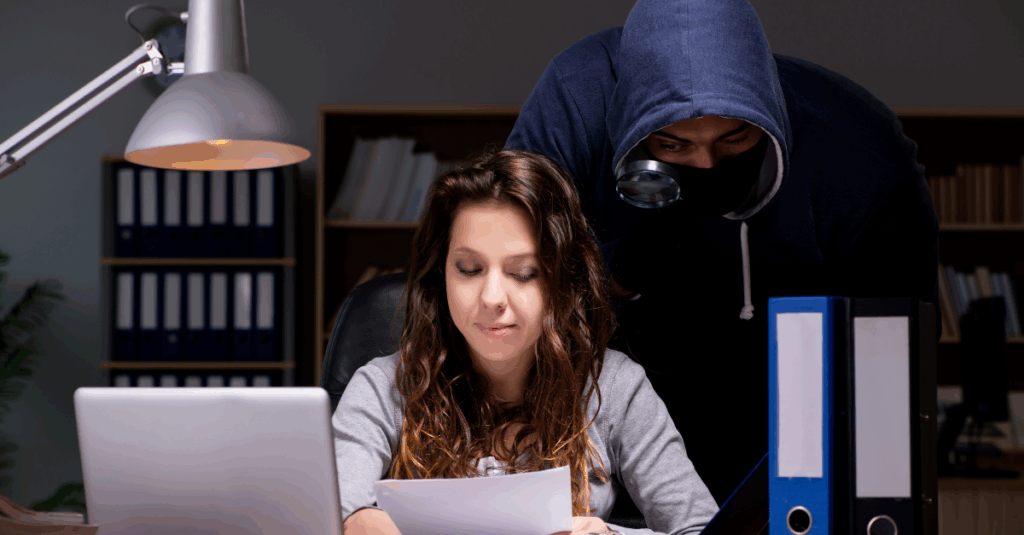
These tactics allow attackers to bypass traditional filters and exploit employees who are busy, distracted, or unaware.
Why SMBs Are Prime Targets
Small businesses are especially attractive to phishing scammers. With limited IT resources, they often lack advanced monitoring tools and staff training programs. Attackers know this and exploit the gap, using phishing as an entry point for ransomware, data theft, or financial fraud.
The cost of a successful phishing attack can be devastating, including downtime, legal fees, regulatory fines, and reputational damage.
Recognizing the Signs of a Phishing Email
Training employees to spot red flags is the first line of defense. Warning signs include:
- Urgent requests for sensitive information.
- Misspelled email addresses or subtle domain changes.
- Unexpected attachments or links.
- Inconsistent branding or grammar errors.
Even the best-trained employees can still be fooled by advanced attacks, which is why layered security is critical.
How to Outsmart Modern Phishing Scams
Combating phishing requires a multi-layered strategy that combines technology, processes, and people.
1. Deploy Advanced Email Security
Traditional spam filters can’t catch AI-generated attacks. Solutions like multi-layered security provide real-time monitoring, AI-driven threat detection, and encryption to block suspicious messages before they reach inboxes.
2. Protect Endpoints with EDR
Every device on your network is a potential entry point. Advanced endpoint detection and response monitors laptops, tablets, and smartphones for suspicious activity and isolates threats before they spread.
3. Back Up Data and Plan for Recovery
Even with strong defenses, no system is 100% immune. A reliable disaster recovery plan ensures your business can quickly restore operations in the event of a ransomware attack.
4. Centralize Device Management
Remote and hybrid teams increase the risk of phishing-related breaches. Solutions like Microsoft Intune enforce security policies across all employee devices and enable remote data wiping if a device is compromised.
5. Use SIEM for Real-Time Monitoring
Modern attacks often hide in plain sight. Advanced tools like Microsoft Sentinel analyze network activity to detect suspicious behavior before it escalates into a breach.
6. Train Employees Regularly
Security awareness training transforms staff from weak links into strong defenses. Programs should include phishing simulations and real-world examples to keep employees alert and prepared.
The Role of Managed IT Services
Technology alone isn’t enough to stop phishing. Businesses also need expert guidance to configure tools, monitor threats, and respond to incidents. A trusted MSP like CMIT Solutions of Bothell and Renton provides:
- 24/7 monitoring of email systems and networks.
- Rapid response to suspicious activity.
- Regular updates and patching to close vulnerabilities.
- Strategic planning to align IT security with business goals.
Managed services ensure your team is protected even as phishing tactics evolve.
Beyond Email: Expanding Your Security Strategy
Phishing attacks are increasingly blended with other cyber threats, including ransomware and cloud-based exploits. A comprehensive plan should also include:
- Unified communication strategies to secure collaboration tools.
- Cloud-first hybrid infrastructures to protect data across cloud and on-premises environments.
- Proactive compliance management to meet regulatory standards and avoid penalties.
These measures create a security framework that goes beyond phishing to protect every aspect of your business.
Conclusion: Stay Ahead of Smarter Scammers
Phishing attacks are evolving faster than ever, but your business doesn’t have to be an easy target. By combining employee training, advanced security tools, and proactive IT support, your team can identify threats and respond before damage is done.
With services like multi-layered cybersecurity, endpoint detection, and strategic managed services, CMIT Solutions of Bothell and Renton helps SMBs outsmart even the most advanced phishing scams keeping your data safe and your business moving forward.