Who Needs Cybersecurity Support?
Any business that uses digital technology to store or access sensitive data needs cybersecurity protection. From small startups to large enterprises, every organization is at risk of cyber threats. Multi-layered solutions-like authentication systems, intrusion detection, and regular security updates-help safeguard data, ensure compliance, and prevent costly breaches.
What Does Cybersecurity Support Include?
At CMIT Solutions, we provide comprehensive cybersecurity support that goes beyond preventing attacks. Our services include threat assessments, firewall implementation, data protection, and user management. We tailor solutions to each business, ensuring round-the-clock security, compliance with regulations, and peace of mind.
Key Components of a Cybersecurity Package
A complete cybersecurity strategy includes:
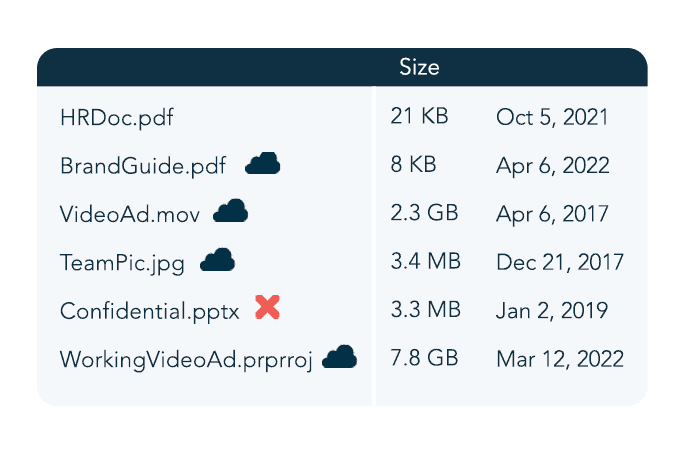
1. Data Compliance: Ensuring adherence to data protection laws and maintaining secure backups.
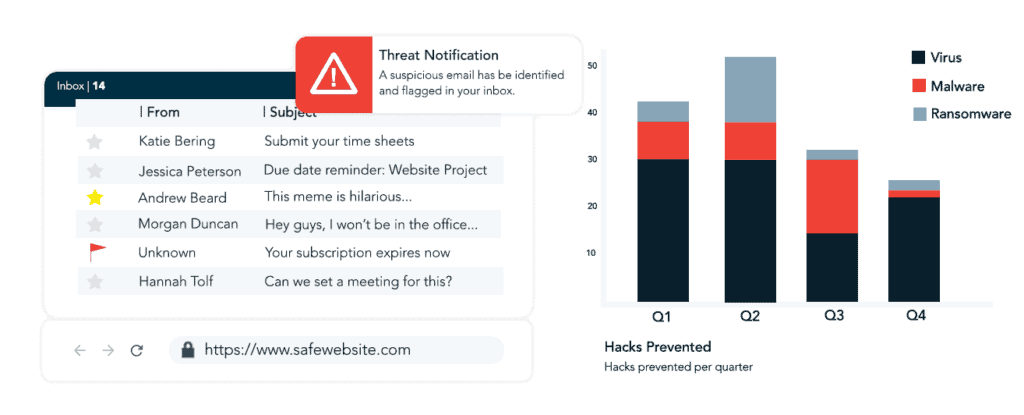
2. Security Software: Using tailored tools to block threats and monitor activity.
3. Awareness Training: Educating employees on phishing, passwords, and safe practices.
4. Risk Mitigation: Preparing for incidents with response plans and penetration testing.
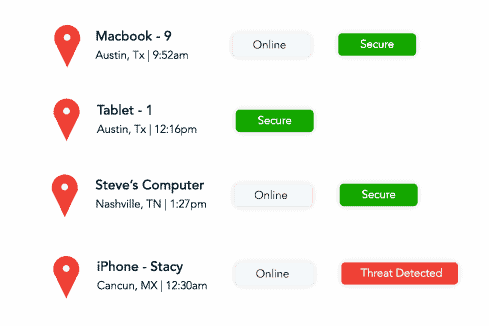
5. Continuous Monitoring: Using SOC and SIEM systems to detect and stop threats in real time.


 Managed Services
Managed Services
 Cybersecurity
Cybersecurity
 Productivity Applications
Productivity Applications
 IT Support
IT Support
 Cloud Services
Cloud Services
 Network Management
Network Management
 Compliance
Compliance
 Data Backup
Data Backup
 Unified Communications
Unified Communications
 IT Guidance
IT Guidance
 IT Procurement
IT Procurement