If you run a financial services firm, you probably feel it in your inbox. A custodian asks for your cybersecurity policy. A client wants proof you encrypt data. A regulator updates guidance. Your insurance carrier raises questions about MFA, backups, and incident response.
None of that is “just paperwork.” In financial services, client trust is the product. When regulators raise the bar, they are really asking one question: Can you protect client data even on your busiest, most chaotic day?
Why the pressure keeps increasing and why it hits small firms hardest
Regulatory expectations are rising because the threats are rising. Financial firms are targeted constantly, not because you are “big,” but because your data is valuable and time-sensitive. Account numbers, tax documents, driver’s licenses, payroll, wire instructions, investment statements, client contact lists. That is a gold mine for criminals.
Large institutions can throw people and budget at the problem. Small and mid-sized firms have to protect the same kinds of data with fewer internal resources, and usually with a patchwork of vendors, apps, and remote work setups. That gap is exactly where issues pop up during audits, renewal reviews, or after an incident.
The good news is that regulators and auditors are not asking you to build a Silicon Valley security program. They want to see that you do the basics consistently, can prove it, and can respond quickly when something goes wrong.
What “secure client data” actually means in plain English
When regulators talk about safeguarding information, it usually boils down to four practical outcomes:
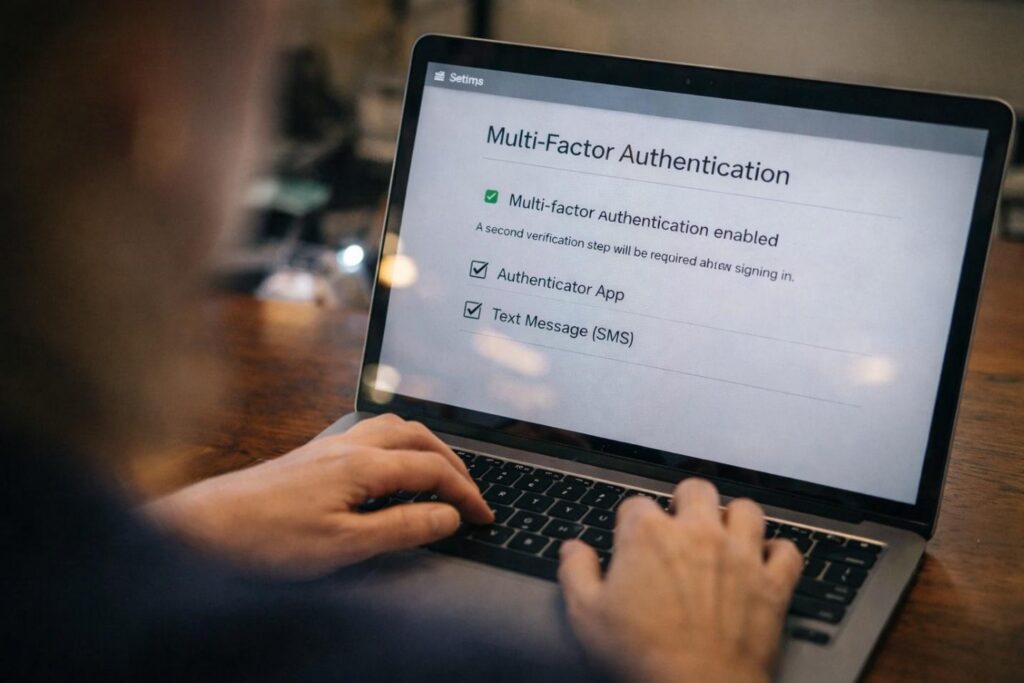
- Only the right people can access data. Access control, least privilege, MFA
- Data stays protected wherever it lives. Encryption, secure email/file sharing, device security
- You can keep working if something breaks. Backups, disaster recovery, business continuity
- You can prove what you did. (Logging, documentation, vendor oversight, training records)
That last one is the sneaky part. Many firms do good things but cannot show evidence quickly. In a review, “we think we have that” is not comforting. Documentation turns your security from a vibe into a verifiable program.
A quick story that feels way too common
A small wealth management firm gets an email that looks like it is from a client: “We changed banks, please update the wire instructions.” The assistant replies, the “client” responds with a PDF, and the assistant opens it. Nothing obvious happens.
Behind the scenes, that attachment steals the user’s email session. The attacker creates an inbox rule to hide replies, watches conversations, then tries to slip in new wire instructions at the perfect moment. Meanwhile, compliance asks for proof of security controls because a partner bank is tightening requirements.
No one at the firm is careless. They are busy. The attack is designed for busy.
This is why managed cybersecurity is becoming the expectation instead of a “nice-to-have.” Consistency beats heroics.
[image prompt: A realistic conceptual photo of an office email inbox on a monitor with a suspicious message highlighted (generic interface, no brand logos), shot with a 24mm lens at f/3.5, natural daylight from a window, slight motion blur from a hand reaching for the mouse, realistic shadows, subtle grain, looks like a real workplace moment.]
The controls regulators expect to see without the jargon
Here are the most common areas that trigger questions, and what “good” looks like for a small or mid-sized firm:
Identity and access management
- MFA turned on everywhere it can be, especially email and remote access
- Strong password policies, ideally with a password manager
- Former employees removed immediately, no shared logins
Email and phishing protection
- Filtering that blocks obvious scams and dangerous attachments
- A clear process for verifying wire requests or banking changes (out-of-band verification is key)
- Staff training that is short, practical, and frequent
Device and endpoint security
- Managed antivirus or endpoint protection with monitoring
- Patch updates handled consistently, not “when someone remembers”
- Full-disk encryption on laptops, especially for hybrid teams
Secure data handling
- Approved methods for file sharing and client document exchange
- Clear rules about personal devices, texting sensitive info, and forwarding emails
- Encryption at rest and in transit whenever possible
Backups and recovery
- Backups that are protected from ransomware immutability or offline copies
- Routine testing, because “we have backups” is not the same as “we can restore”
- A plan for what happens if your primary systems go down for a day
Vendor management
- Knowing which vendors touch client data
- Basic documentation: contracts, security summaries, and who is responsible for what
- A process to offboard vendors, not just onboard them
This is also where many firms start looking at [cybersecurity companies in chicago] because they need local support that can help with both the technology and the evidence trail.
The biggest mistake: treating compliance and security as separate projects
Security is what you do. Compliance is how you prove it and repeat it.
If those are separate efforts, you end up with one of two problems:
- You have a nice policy binder, but the real environment does not match it.
- You have decent tools, but no documentation, no testing, and no consistent process.
The most effective approach is to build a simple, living routine: monthly patch reporting, quarterly access reviews, regular backup tests, and a lightweight incident response plan that names who does what. It is not glamorous, but it is exactly what reviewers want to see.
A practical “90-day plan” for financial firms
If you want a clear starting point, aim for these outcomes in the next three months:
- Lock down email: MFA, conditional access where possible, and phishing protection tuned properly
- Standardize devices: encryption, patching, and endpoint protection across all laptops and desktops
- Test backups: perform a real restore test, not just a checkbox
- Document the essentials: security policy summary, access review process, vendor list, incident response contacts
- Train people with realism: short sessions using examples your team actually sees (wire fraud, fake DocuSign, “sharepoint” links)
If you do nothing else, prioritize email security and backups. Those two areas alone prevent a huge percentage of expensive, business-stopping incidents.
Where a local IT partner fits
Many financial firms do not need a full-time security team. They need a reliable [managed service provider] that can run the basics consistently, keep tools updated, watch for suspicious activity, and help produce the documentation you get asked for.
At CMIT Solutions of Oak Park, we help financial services teams tighten security without turning your staff into IT people. That includes practical safeguards like MFA and endpoint protection, business-friendly backup and recovery, and the reporting you need when an auditor, insurer, or client asks, “Can you prove it?”
If you are feeling the regulatory squeeze, let’s turn it into a clear plan. Reach out to CMIT Solutions of Oak Park and we will review your current setup, identify the biggest risk gaps, and map out next steps that fit your firm’s size, workflow, and compliance reality.