Artificial Intelligence (AI) is transforming how businesses operate — and it’s also changing how cybercriminals attack.
And the result? A growing fear among business owners about how to protect their companies from threats they don’t fully understand.
So the critical question becomes: Is your business prepared for AI-powered cyberattacks? This uncertainty is exactly why many businesses — especially SMBs — are now turning to cybersecurity consulting services for expert guidance.
This guide simplifies the complexity of AI-driven cyber risks — helping you assess your real readiness against evolving AI threats. Let’s begin with what AI-powered cyberattacks actually mean.
What is an AI-Powered Cyberattack?
An AI-powered cyberattack is an attack where criminals use AI to plan, refine, and execute malicious actions.
Instead of relying only on manual techniques, cybercriminals deploy algorithms that can:
- Analyze patterns.
- Mimic human behavior.
- Personalize messages.
- Automate attacks at a massive scale that once required human effort.
- Launch more targeted campaigns.
- Run multiple attack variations simultaneously.
➔ These capabilities make their attempts faster, more accurate, and significantly harder to detect — dramatically increasing the success rate of cyber intrusions.
Now, this brings us to an important question: How is AI being used in cyberattacks?
Cybercriminals now use AI to:
- Scan systems for weaknesses.
- Generate highly convincing phishing messages that are nearly impossible to spot.
- Create malware that constantly rewrites itself to avoid detection.
- Launch scams that unfold at lightning speed.
- Bypass security tools.
- Continuously adjust their methods based on the defenses they encounter.
Next, let’s explore why your current defenses may fall short against AI threats.
Why Your Current Security Measures Might Not Be Enough
Here’s what makes today’s threat landscape so different: AI has essentially democratized cybercrime.
Previously, creating sophisticated malware required years of technical expertise, but now, criminals with few technical skills can use AI to conduct operations that once took expert hackers years to develop.
➔Since the launch of advanced AI models in November 2022, smishing, vishing, and phishing attacks have surged by 1,265% — demonstrating the intensity of AI-powered cyberattacks.
- In the past, you might have spotted poor grammar in phishing emails, but AI-generated content eliminates these red flags — making messages flawless and personalized.
- AI-driven messages are so sophisticated that they are indistinguishable from legitimate communications, showcasing increased sophistication and stealth.
Not only do these attacks feature heightened intelligence, but they also operate at an unprecedented scale — allowing an attacker to launch numerous assaults simultaneously. This increased volume and speed create a level of pressure on defenses that hasn’t been seen before, overwhelming your current systems.
For years, cybersecurity has relied on inadequate traditional defenses — like rule-based systems and signature detection on firewalls. But these methods are no longer enough, as AI malware can alter its structure to bypass security tools that rely on pattern recognition.
With 60% of IT professionals feeling their organizations are unprepared for AI-generated threats, the underpreparedness of businesses is a critical vulnerability.
“AI has changed the balance of power in cybersecurity — exploiting gaps that traditional systems can’t recognize.”
Next, let’s uncover how AI-driven attacks are quietly infiltrating your routine operations and exposing hidden vulnerabilities.
Also Read: How Gamification in Cybersecurity Training Changes the Game
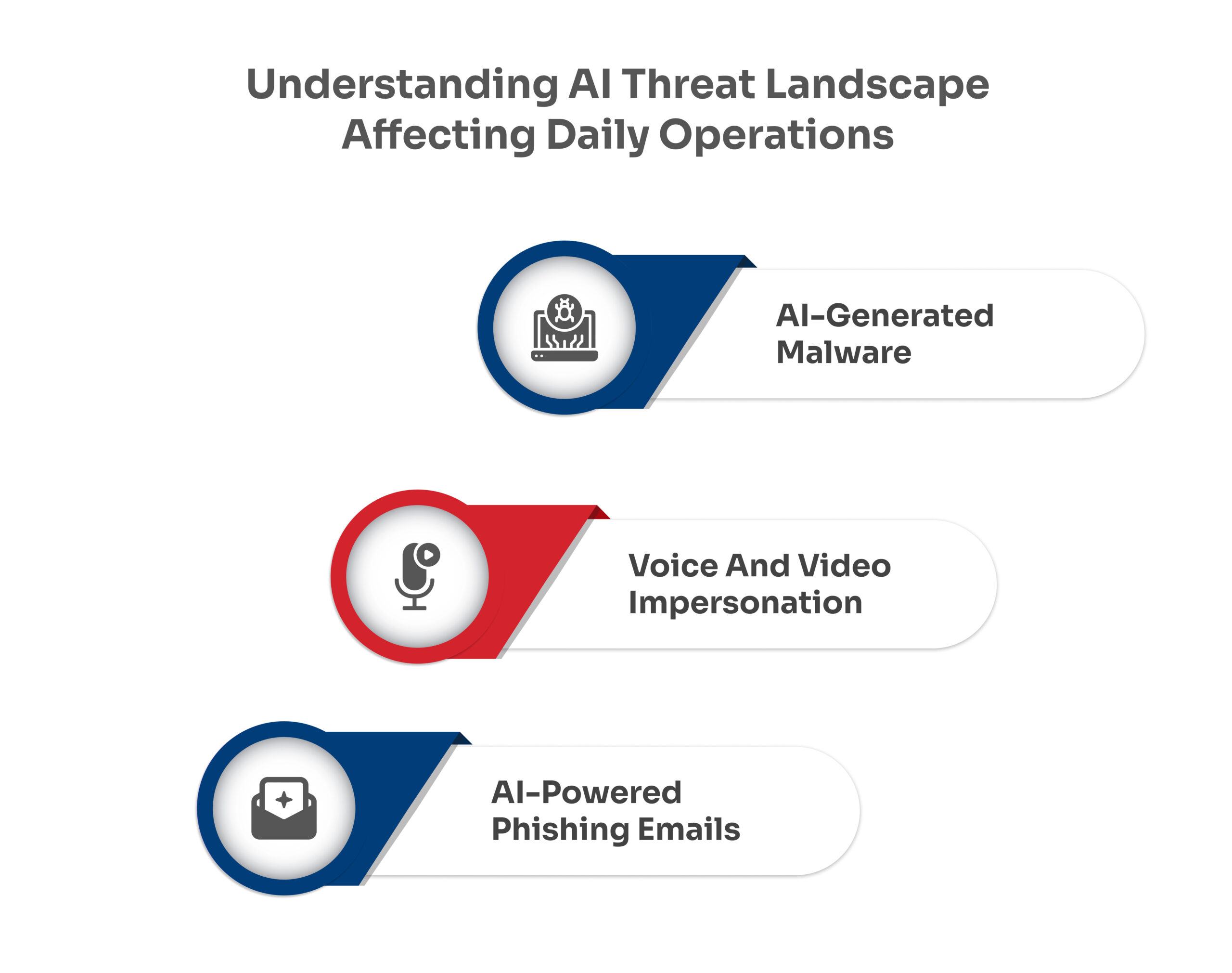
Common AI Threats Targeting Your Daily Operations
Modern attacks are no longer obvious — they are intelligent, adaptive, and personalized.