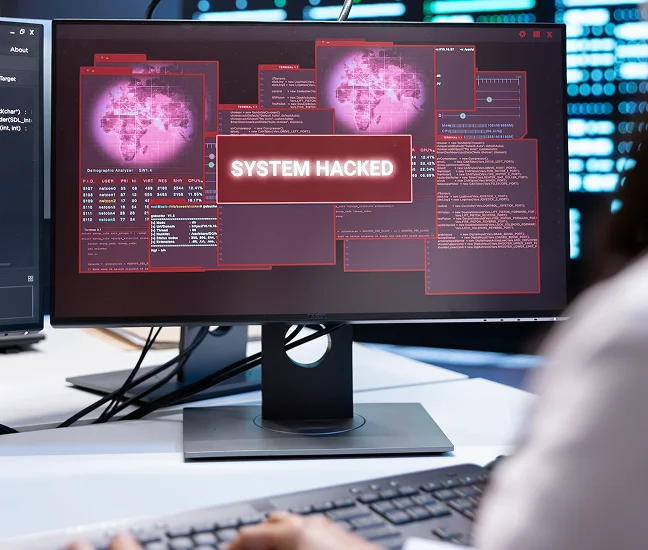
Is Your Winchester VA Business Protected From Cyberattacks?
61% of small businesses face cyberattacks annually – and Winchester VA businesses are no exception. CMIT Solutions of Northern Shenandoah Valley provides multi-layer cybersecurity: ransomware protection, endpoint detection, dark web monitoring, and 24/7 threat response for Top of Virginia and Eastern Panhandle of WV businesses.
- Ransomware protection and incident response
- Endpoint detection and response (EDR)
- Email security and anti-phishing filtering
- Dark web monitoring for business credentials
- 24/7 threat monitoring and alerting
- HIPAA and CMMC compliance-ready
- Cyber insurance readiness support
- Winchester VA local team – Top of Virginia and Eastern Panhandle of WV