Recent flash floods highlight need for preparedness and continuity.
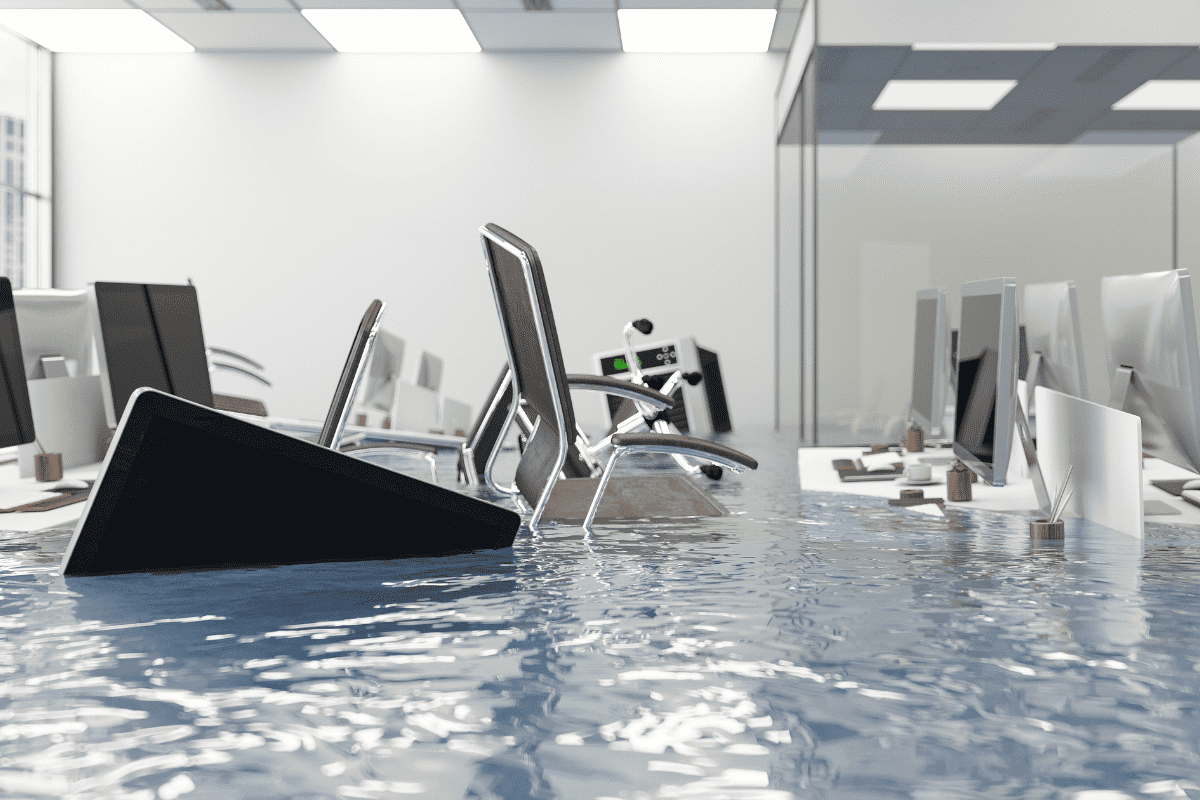
Recent flooding in Vermont, New Hampshire, and New York has devastated the area’s bucolic towns and tight-knit communities. The primary focus over the last two weeks has been saving lives and protecting property. But as floodwaters recede and businesses take stock of the damage, many will realize they weren’t prepared for a natural disaster of such magnitude.
In an increasingly interconnected world, where computers and technology systems have become an integral part of our daily lives, protecting these assets from unforeseen disasters is paramount. The flash floods in Vermont and surrounding areas highlight the vulnerability of both our physical and digital infrastructure.
CMIT Solutions has spent the last 25 years helping businesses across North America safeguard their systems and protect their data from natural and manmade disasters. We’ve learned a few lessons over the years and how important it is to take proactive measures that mitigate risk and ensure business continuity. Here’s what we regularly share with businesses that find themselves in harm’s way:
- Prioritize the preservation of critical business data. In the face of flash floods and other natural disasters, physical infrastructure like computers, servers, and offices themselves often bear the brunt of destruction. Such events pose an immediate threat to the integrity and accessibility of critical data. Companies, organizations, and individuals rely on computers, hard drives, and cloud storage applications to house and protect valuable information, ranging from financial records and customer data to intellectual property and research findings. Failure to protect these systems before a disaster strikes can lead to irretrievable loss, compromised privacy, operational disruptions, and long-term financial setbacks.
- Implement and test preparedness and continuity protocols. For businesses, the ability to continue operations during and after a disaster is crucial for survival. Technology lies at the heart of most modern organizations, facilitating communication, business transactions, and day-to-day operations. Without a robust disaster preparedness and business continuity plan, companies risk extended downtime, lost productivity, damaged reputations, and potential closure. Coming up with a plan in advance to safeguard computers and technology from flash floods and other disasters should be seen as a necessary investment in the resilience and continuity of business operations.
- Stem the tide of financial losses. Recovering from a disaster can be an expensive endeavor—especially for small businesses. The costs associated with replacing damaged or destroyed systems can be significant, and the potential loss of revenue during a recovery period only compounds the problem. Implementing straightforward preventive measures in advance—raising equipment off the ground, using waterproof enclosures, and creating off-site data backups—is the first step to minimizing the financial impact of disasters. Understanding the ins and outs of your insurance coverage before disaster strikes is also important. The bottom line is you should know how your safety net will work in case of unforeseen events. That way, you can be prepared in advance to maintain financial stability.
- Treat sensitive or private information with the care it deserves. The protection of private business data is incredibly important. Believe it or not, many hackers and bad actors will actually use natural disasters like flash floods, fires, or hurricanes to try and execute elaborate schemes involving cybercrime or identity theft. Flooded or damaged computers and hard drives must be disposed of properly to eliminate the threat of data loss or unauthorized access. Devices and systems that remain in use should be protected by end-to-end data encryption, strong passwords, and access controls, preserving privacy and trust in the event of a disaster.
- One company’s recovery can contribute to greater community resilience. Natural disasters not only impact individual businesses and organizations but also the broader communities that they exist in. A robust and interconnected technological ecosystem is vital for effective emergency response and recovery efforts. From coordinating relief operations to disseminating critical information, computers, smartphones, Internet connections, and other technologies play a central role in disaster management. Protecting these assets ensures that people can communicate during crises, lives can be saved when the worst happens, and communities can bounce back faster and restore normalcy in the aftermath of a crisis.
The recent flash floods in Vermont, New Hampshire, and New York serve as a stark reminder of how vulnerable we are to natural disasters. Protecting business data and technology systems isn’t just an afterthought during such a crisis—instead, it’s a collective responsibility that helps communities maintain stability and resilience in the face of immense challenges.
CMIT Solutions has decades of experience helping businesses of all sizes to adopt proactive measures, implement disaster preparedness plans, execute data backup strategies, and enhance cybersecurity before, during, and after emergencies. We can minimize the impact of flash floods and other disasters on digital infrastructure and help your rest easy knowing that computers are safe, data is secure, and the path ahead leads to a more resilient and connected future.
Contact us today if you need help preparing for or responding to a natural disaster.