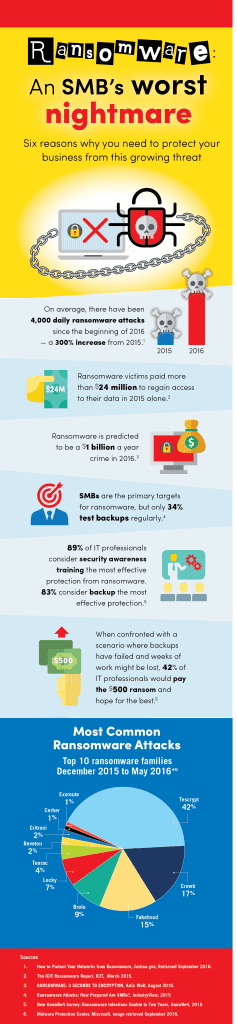
3 Ways to Protect Yourself from Ransomware
Basic security protocols will keep you protected, but only up to a point — and ransomware architects are constantly working to sneak their handiwork past any and all systems working to stop it. But with stronger defenses like proactive monitoring, Internet traffic analysis, and content filtering, preventing ransomware while keeping your data safe and accessible is possible.
We recommend three basic steps to help keep your business safe from Ransomware attacks:
1) Back up, back up, back up.
Hackers that use ransomware are counting on a business or an individual to NOT back up their data (as only about 50% of organizations do). If ransomware encrypts a critical file, and the only way to access it is to pay a ransom, most companies will capitulate. But if you have a dedicated remote backup (hopefully conducted at least once a day), you can ignore the hackers’ demands and simply just restore your data without having to pay extra for it.
2) Implement layered network security.
CMIT Solutions has the ability to deliver heightened security that analyzes Internet traffic for malware, botnets, and phishing attempts before they affect your system. By identifying targeted attacks, blocking threats both on local networks and mobile devices, and enforcing acceptable use policies through content filtering, the proactive monitoring or “umbrella” approach can deliver an unprecedented level of security. Of course, no one layer of security provides surefire protection, which is why we also specialize in…
3) Train your employees to beware of ransomware threats.
Enforcing the rule that no one should click on any link or attachment unless they are expecting it from a specific contact is a good start. But so is basic training in the ins and outs of malvertising, the dangers of social engineering, and the increasing infiltration of phishing emails. The more aware your employees are, the safer your company will be.
Looking for help to put all three of these steps to work for your organization? Contact a trusted IT adviser like CMIT Solutions. For us, proactive monitoring, backup and disaster recovery, business continuity, data encryption, and secure cloud storage are crucial to surviving (and thriving) in today’s complicated IT world. We are here to defend your network, secure your data, and empower your staff to be more productive. At CMIT, we worry about your IT so that you can worry about the success of your business.